
By The Maritime Executive 05-15-2020 04:27:42
The confusion attending the COVID-19 pandemic has created new opportunities for cybercrime, particularly cyberattacks targeting the human element. Fraudulent “phishing” attempts and similar deceptive tactics are an omnipresent cyber threat, and they can be even more potent in times of heightened uncertainty and stress. According to Lloyds Register’s cybersecurity outfit, Nettitude, about 80 percent of current email-based threats attempt to exploit COVID-19-related communication.
To find out more about how hackers are exploiting the outbreak to deceive employees and gain access to corporate IT systems, we spoke with an expert – Chris Oakley, Nettitude’s VP of Technical Services for the Americas. In addition to an update on the facts on the ground, Oakley provided an extensive list of actions that maritime employers and staffmembers can take to minimize risk – and maximize the success of their response in the event of a cyberattack.
MarEx: Themed phishing attacks (like the new COVID-19-related activity) take advantage of unsuspecting staffmembers. What should employees be trained to watch out for in their own browsing/email activity to reduce risk?
• Be aware that threat actors will use current affairs as means to target people with increased success. We see this every time there’s a natural disaster, national security incident or similar event. Awareness is the first step.
• Are you expecting the suspicious communication? If not, proceed with caution.
• If it purports to come from a known source, e.g. your own organization, be aware that this can be forged.
• Are you being prompted to download and open or run a file, visit a third-party website, or submit information of any kind? If so, proceed with caution and speak to your line manager or other internal authority to verify the legitimacy of the communication. Don’t be afraid to report.
• Only use your work laptop for work purposes.
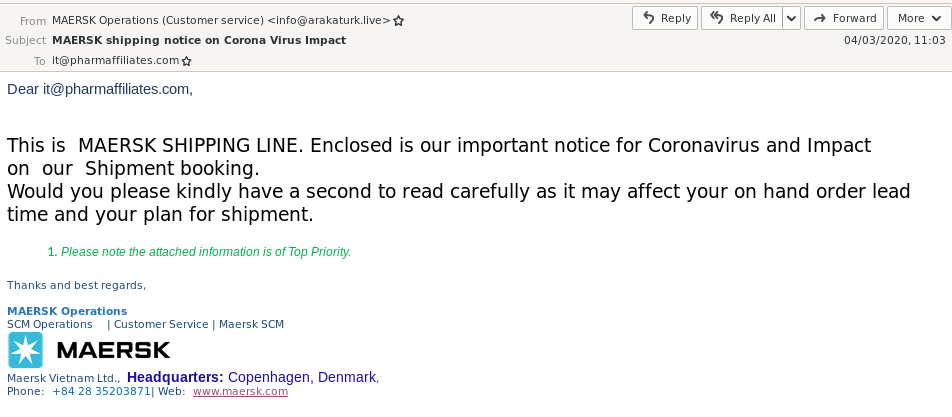
Above, an example of a malicious coronavirus-themed email thread (Nettitude)
MarEx: What kind of technical measures (for example, ProofPoint) can companies implement to reduce the risk of having their own employees accidentally let in a hacker? And how can Nettitude help?
• Technology is an important part of a robust security posture, although not the only part. You can’t rely solely on technology. People, process and technology are all relevant.
• There should be strategy behind any technology deployment. Aligning to a framework such as NIST CSF is useful.
• We recommend, at a minimum, technologies that facilitate asset identification, protection, detection, response and recovery. (To reiterate, these things require more than just technology.)
• Quick technology wins include email gateway technology that is designed to detect and block phishing emails; endpoint detection and response technology to help prevent malicious software from gaining a foothold; and well-configured firewalls that focus on restricting what traffic can leave the network, not just enter.
• In addition to phishing, a common method of entry for an attacker is attacking software vulnerabilities, especially in internet-facing infrastructure. Robust first- and third-party patch management technology should be in place, as well as following principles such as least privilege, so that attackers need to work harder to move through your estate.
MarEx: If a company should experience a significant cybersecurity breach – like a malware attack – are there immediate response steps that they should take for containment and damage control?
• Be proactive: plan what you will do in the event of a breach before it happens. This way, you don’t have to work it out in the heat of the moment when time is short and a robust response is critical.
• Run through a number of scenarios as part of this – e.g. ransomware, data theft, phishing, denial of service, etc. Where do roles and responsibilities lie? What process will be followed?
• In the event of breach detection, the immediate concerns will include determining the scope and scale of the compromise, as well as if the threat is still active.
• Containment may involve isolating assets – e.g. if a laptop or other lower importance asset is suspected or known to be compromised, an appropriate immediate action is to remove its network connection to prevent further impact.
• Gather as much information as possible. This will likely include interviewing end users. It is very important to foster a culture of education and not fear. An end user fearing the repercussions of revealing what they did that could have accidentally facilitated the breach is not likely to help.
• It is not usually a good idea reboot or shut down compromised machines. Important evidence of the breach may exist in memory only, which gets wiped on reboot and shutdown.


